Top Veracode Alternatives for Modern CI/CD Pipelines
In modern software development, speed and security must work together. Traditional scanning after deployment slows down release cycles and raises risk. Developers and security teams are now using shift-left tools that integrate directly into CI/CD pipelines. These tools detect vulnerabilities early and allow for immediate fixes.
This article highlights the best Veracode alternatives that focus on security integrated into pipelines, helping teams maintain fast, secure, and reliable continuous delivery.
Top CI/CD-Focused Platforms
Integrating security into CI/CD pipelines ensures that vulnerabilities are spotted during builds and testing, not after deployment.
The benefits include:
- Early detection of vulnerabilities within builds
- Automated security checks in CI/CD workflows
- Real-time feedback for developers
- Centralized visibility across pipelines and environments
- Consistent policy enforcement from the first commit
Integrating security early prevents issues from compounding and reduces costly fixes later. It also encourages a culture where developers own security responsibilities, making the process faster and more efficient.
- Aikido Security

Aikido Security is built for fast CI/CD pipelines, integrating security into every step of the build and deployment process. It combines SAST, DAST, dependency scanning, and IaC checks, giving developers real-time, actionable feedback.
Key Features
- Pipeline-native integration: Works with Jenkins, GitHub Actions, GitLab, CircleCI, and more
- Real-time developer feedback: Fix vulnerabilities during coding and builds
- All-in-one coverage: SAST, DAST, dependency scanning, secrets, and IaC
- Automated scanning: Continuous and on-demand within pipelines
- Prioritization of actionable risks: Reduces noise and focuses on critical vulnerabilities
- Remediation guidance: Clear, step-by-step instructions for developers
- Centralized dashboards: Track pipeline security trends and risk over time
- Policy enforcement: Security rules applied consistently across projects
- Scalability: Handles multiple repositories, microservices, and environments
- Cross-team collaboration: Allows developers and security teams to coordinate fixes efficiently
Weaknesses
No notable weaknesses.
Why teams choose it
Teams favor Aikido for its complete CI/CD integration, automated feedback, and actionable guidance without slowing down development.
- GitLab
GitLab’s DevSecOps platform offers strong shift-left security tools directly within the CI/CD pipeline. Teams can run SAST, DAST, dependency and container scanning, and IaC scanning automatically with each build, all from the GitLab interface.
Key Features
- Native CI/CD integration: Security tests run as part of the standard GitLab pipeline.
- SAST and DAST scanning: Detect vulnerabilities in code and running applications.
- Dependency scanning: Identifies vulnerable libraries and packages early.
- Container scanning: Checks Docker and Kubernetes artifacts during the build process.
- IaC scanning: Finds misconfigurations in cloud deployment files.
- Automated pipelines: Security gates automatically block unsafe builds.
- Merge request insights: Security results are displayed directly in merge requests.
- Reporting dashboards: Track risks over time across projects.
Weaknesses
GitLab-centric: Best suited for teams that already use GitLab for CI/CD.
Complex configuration: Some advanced security tests may require tuning of the pipeline.
Why teams choose it
Teams using GitLab appreciate having security integrated into their existing CI/CD workflows without the need for separate tools or dashboards.
- Mend.io
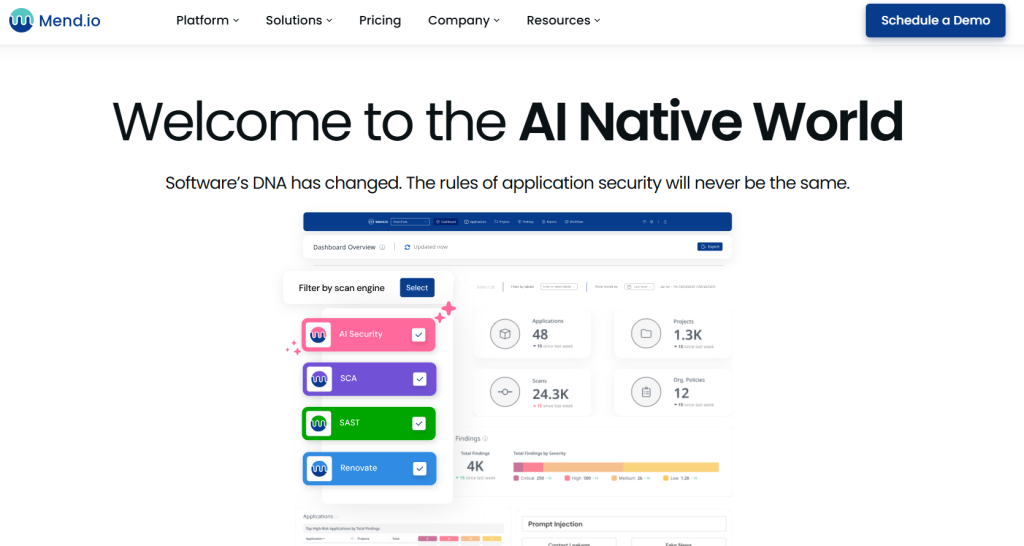
Mend.io focuses on spotting and managing open-source vulnerabilities during CI/CD workflows. It offers automated alerts and remediation.
Key Features
- Continuous scanning of open-source libraries
- CI/CD integration: Jenkins, GitHub Actions, Azure DevOps
- Automated alerts for new vulnerabilities
- Remediation guidance: Suggested fixes and pull requests
- Policy enforcement: Block risky components in the pipeline
- Centralized dashboards: Visibility of open-source risk across builds
- Security dashboards: Monitor trends across pipelines
- Developer collaboration: Assign issues and track fixes within workflow
Weaknesses
- Limited non-open-source coverage: Focused mainly on open-source vulnerabilities
- Potential false positives: Some alerts may require manual verification
Why teams choose it
Teams select Mend.io for effective open-source security. It helps developers fix vulnerabilities before deployment.
- Contrast Security
Contrast Security integrates security checks into CI/CD pipelines. It combines static, dynamic, and runtime analysis for ongoing protection.
Key Features
- Pipeline integration: Supports Jenkins, GitLab, GitHub Actions, and more
- Real-time vulnerability feedback for developers
- SAST, DAST, and IAST coverage for complete security
- Remediation guidance: Step-by-step instructions
- Policy enforcement: Maintain security and compliance standards
- Centralized dashboards: Track risk trends across applications
- Scalability: Works in cloud-native and containerized environments
- Pipeline alerting: Immediate notification of high-risk vulnerabilities
- Team collaboration tools: Assign issues, track fixes, and coordinate across dev and security teams
Weaknesses
- Resource usage: Runtime checks can increase pipeline build times
- Complexity: Full integration can require additional configuration for large pipelines
Why teams choose it
Teams value Contrast Security for continuous, automated security in CI/CD pipelines. It helps developers find and fix vulnerabilities quickly.
Final Thoughts
Security must be built into CI/CD pipelines, not added after deployment. Shift-left AppSec solutions provide automation, usable insights, and seamless pipeline integration. This setup allows teams to deliver secure code faster.
Embedding security into every build helps catch vulnerabilities early, minimizes risks, and keeps development speed high. Modern pipelines perform best when security is integrated, automated, and easy for developers. This setup enables teams to ship applications safely and with confidence.
By adopting these methods, organizations can cut down on expensive post-deployment fixes, improve team collaboration, and maintain continuous compliance without slowing down innovation. Security becomes a natural part of the development workflow rather than an afterthought. This shift gives teams peace of mind while speeding up delivery.